Cybersecurity Threats 2026: Financial Impact on U.S. Infrastructure
Anúncios
The digital landscape is constantly evolving, and with it, the sophistication and frequency of cyber threats. As we look towards 2026, the convergence of advanced technologies, geopolitical tensions, and an increasingly interconnected world presents an unprecedented level of risk to critical U.S. infrastructure. While the immediate operational disruptions caused by cyberattacks are often highlighted, the long-term and pervasive cybersecurity financial impact is a far more insidious and devastating consequence that demands urgent attention. Understanding these financial ramifications is paramount for developing robust defense strategies and ensuring national resilience.
Anúncios
In this comprehensive analysis, we will delve deep into the projected cybersecurity threats for 2026, meticulously examining how global breaches are set to inflict significant financial damage on various sectors of U.S. infrastructure. From energy grids and financial institutions to transportation networks and healthcare systems, no sector is immune. We will explore the direct costs associated with breaches, such as incident response, data recovery, and regulatory fines, alongside the more elusive indirect costs, including reputational damage, loss of intellectual property, and decreased market capitalization. Furthermore, this article will outline proactive measures and strategic investments necessary to mitigate these escalating risks and safeguard the economic stability of the United States.
The Evolving Threat Landscape: What 2026 Holds
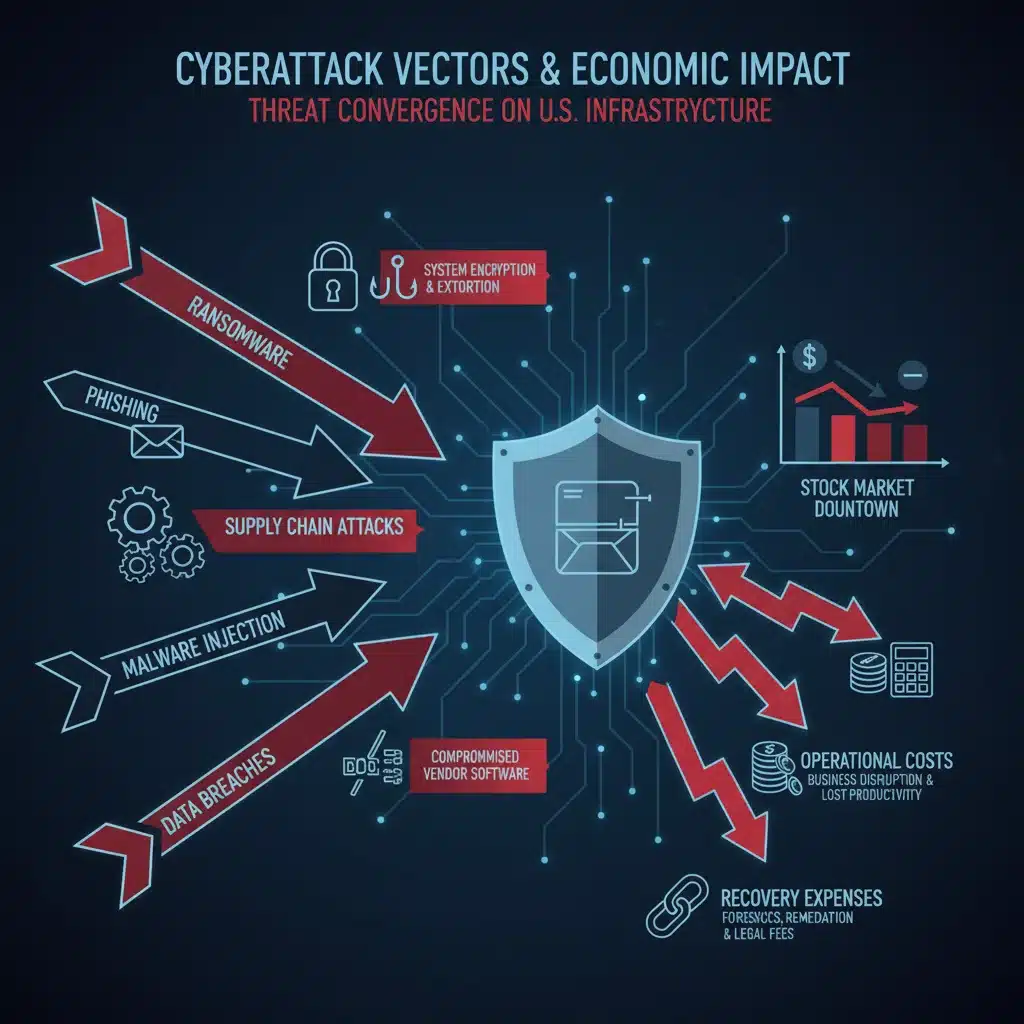
The year 2026 is anticipated to be a watershed moment in cybersecurity, characterized by several key trends that will amplify the cybersecurity financial impact on U.S. infrastructure. Nation-state actors will continue to refine their offensive capabilities, targeting critical infrastructure not just for espionage but for disruptive and destructive purposes. The rise of sophisticated ransomware-as-a-service (RaaS) models will democratize access to advanced attack tools, enabling a wider array of malicious actors to launch devastating campaigns. Moreover, the increasing reliance on complex supply chains will introduce new vulnerabilities, as a single compromise in a vendor’s system can ripple through an entire ecosystem.
Anúncios
Advanced Persistent Threats (APTs) and Nation-State Activities
Nation-state-sponsored groups, often referred to as Advanced Persistent Threats (APTs), represent the pinnacle of cyber warfare capabilities. Their objectives extend beyond mere data theft, encompassing industrial espionage, intellectual property theft, and the disruption or destruction of critical infrastructure. In 2026, these actors are expected to leverage even more sophisticated techniques, including zero-day exploits, AI-powered reconnaissance, and highly evasive malware. The financial implications of such attacks are multifaceted: direct costs for remediation, potential loss of sensitive national security information, and the erosion of public trust in government and essential services. The recovery from a targeted APT attack on, for instance, a major power grid, could run into billions of dollars, encompassing not only repair costs but also economic losses from widespread outages and the subsequent ripple effects on businesses and daily life.
The Proliferation of Ransomware 2.0
Ransomware has already proven to be a highly profitable and disruptive form of cybercrime. By 2026, we anticipate a new generation of ransomware, often dubbed ‘Ransomware 2.0,’ which will incorporate advanced tactics such as double extortion (exfiltrating data before encrypting it, threatening to release it if the ransom isn’t paid), triple extortion (adding DDoS attacks or notifying customers/partners), and attacks targeting operational technology (OT) systems within industrial control environments. The cybersecurity financial impact of these attacks is staggering. Beyond the ransom payment itself, organizations face colossal costs for business interruption, system recovery, forensic investigations, legal fees, and reputational damage. Small and medium-sized businesses (SMBs) are particularly vulnerable, often lacking the resources to defend against or recover from such sophisticated attacks, potentially leading to bankruptcy.
Supply Chain Compromises: A Growing Economic Threat
The interconnectedness of modern supply chains, while efficient, also presents a significant attack surface. A single vulnerability in a widely used software component or a third-party vendor can be exploited to compromise numerous organizations downstream. The SolarWinds attack served as a stark reminder of this danger. In 2026, attackers will increasingly focus on exploiting these supply chain weaknesses, understanding that compromising one trusted link can grant access to a multitude of high-value targets. The financial consequences include not only the direct costs borne by the primary victim but also the cascading economic losses experienced by all affected entities, leading to widespread operational paralysis, loss of customer confidence, and significant remediation expenses across an entire industry.
Direct Financial Impacts of Cyber Breaches on U.S. Infrastructure
The financial toll of cyberattacks on U.S. infrastructure is often underestimated. While headlines focus on data stolen or systems encrypted, the true cost extends far beyond these immediate metrics. Direct costs are quantifiable expenses incurred as a direct result of a cyber incident.
Incident Response and Remediation Costs
Once a breach is detected, organizations must immediately activate incident response protocols. This involves engaging cybersecurity forensics experts, internal security teams, and potentially external consultants to identify the scope of the breach, contain the threat, eradicate the malicious presence, and restore affected systems. These efforts can be incredibly expensive, particularly for large-scale infrastructure attacks that require extensive downtime and specialized expertise. The cost of forensic analysis, system rebuilding, and implementing new security controls can quickly escalate into millions of dollars, directly contributing to the significant cybersecurity financial impact.
Data Recovery and System Restoration
For many infrastructure sectors, data integrity and system availability are paramount. A cyberattack can lead to data corruption, deletion, or encryption, necessitating costly recovery efforts. This might involve restoring from backups, which itself can be a time-consuming and resource-intensive process, or in extreme cases, rebuilding entire databases and operational systems from scratch. The longer systems are down, the greater the operational losses, which translates directly into financial strain. For critical infrastructure like energy grids or water treatment plants, prolonged outages can have catastrophic societal and economic consequences, far exceeding the direct cost of data recovery.
Regulatory Fines and Legal Expenses
With an increasing number of data privacy regulations (e.g., GDPR, CCPA, HIPAA) and industry-specific compliance mandates (e.g., NERC CIP for energy), organizations found to be in violation due to a cyber breach can face substantial regulatory fines. These penalties can range from hundreds of thousands to hundreds of millions of dollars, depending on the severity of the breach, the number of affected individuals, and the organization’s compliance posture. Furthermore, affected individuals or organizations may file lawsuits, leading to significant legal expenses for defense, settlements, and potential class-action payouts. These legal and regulatory burdens add another substantial layer to the overall cybersecurity financial impact.
Reputational Damage and Loss of Customer Trust
While harder to quantify immediately, reputational damage is a severe long-term financial consequence of a cyber breach. When critical U.S. infrastructure organizations suffer an attack, public trust can erode rapidly. Customers, citizens, and investors may lose confidence in the organization’s ability to protect their data or provide reliable services. This loss of trust can lead to customer churn, reduced market share, difficulty attracting new business, and a decline in investor confidence, all of which manifest as significant financial losses over time. For public utilities or government services, this can also translate into decreased public support and political ramifications.
Intellectual Property Theft and Competitive Disadvantage
For sectors involved in research, development, or advanced manufacturing, cyberattacks can lead to the theft of valuable intellectual property (IP), trade secrets, and proprietary information. This can result in a significant competitive disadvantage, allowing rivals to replicate innovations, undercut pricing, or gain market share. The financial loss from IP theft is often incalculable, as it represents the future earning potential of products, services, and innovations. Nation-state actors are particularly keen on this type of espionage, aiming to bolster their own industrial capabilities at the expense of U.S. companies, thereby amplifying the long-term cybersecurity financial impact on entire industries.
Indirect and Long-Term Financial Repercussions
Beyond the immediate and quantifiable costs, cyberattacks trigger a cascade of indirect financial repercussions that can undermine an organization’s stability and growth for years.
Business Interruption and Lost Revenue
Perhaps one of the most significant indirect costs is business interruption. When systems are compromised, operations halt or are severely degraded. This can lead to lost sales, missed deadlines, production stoppages, and inability to provide essential services. For sectors like manufacturing or finance, even a few hours of downtime can translate into millions of dollars in lost revenue. The cascading effect on interconnected businesses within the supply chain further amplifies these losses. Calculating the full extent of lost business opportunities and revenue due to prolonged outages is a complex but critical component of understanding the total cybersecurity financial impact.
Increased Insurance Premiums and Security Investments
Organizations that have experienced a cyber breach often face significantly higher cybersecurity insurance premiums in subsequent years. Insurers view them as higher risk, leading to increased operational costs. Furthermore, to prevent future attacks and restore confidence, organizations are compelled to make substantial new investments in cybersecurity technologies, personnel, and training. While these investments are necessary, they represent a significant financial burden, diverting resources that could otherwise be used for innovation or growth. This ongoing expenditure becomes a persistent financial drain following a major incident.
Devaluation of Assets and Market Capitalization
Publicly traded companies that suffer significant cyberattacks often experience a decline in their stock price. Investor confidence can plummet, leading to a devaluation of the company’s market capitalization. This financial hit can be substantial and take a long time to recover, impacting shareholders and the company’s ability to raise capital. For infrastructure entities, even if not publicly traded, a perceived weakness in cybersecurity can lead to reduced credit ratings, making borrowing more expensive and hindering essential development projects. This broadens the scope of the cybersecurity financial impact to the broader economic health of the nation.
Sector-Specific Financial Vulnerabilities in U.S. Infrastructure
Each sector of U.S. critical infrastructure possesses unique vulnerabilities and faces distinct financial risks from cyber threats.
Energy Sector: Grid Stability and Economic Disruption
The energy sector, encompassing electricity, oil, and gas, is a prime target for cyberattacks due to its vital role in national security and economic stability. A successful attack could lead to widespread power outages, disrupting businesses, homes, and critical services. The financial impacts would include direct repair costs, lost revenue for energy providers, and massive economic losses from businesses unable to operate. Furthermore, restoring trust in the grid’s resilience would require significant investment and time, cementing a profound cybersecurity financial impact.
Financial Services: Data Integrity and Market Confidence
Financial institutions are constantly under siege from cybercriminals seeking to steal funds, personal financial data, and manipulate markets. Breaches in this sector can lead to direct financial losses through fraud, extensive remediation costs, and severe regulatory fines. Beyond that, a loss of confidence in the integrity of financial systems could trigger market instability, impacting investment, credit, and the broader economy. The interconnectedness of global financial markets means a breach in one institution can have ripple effects worldwide.
Transportation Networks: Supply Chain Chaos and Operational Costs
Airports, railways, shipping ports, and logistics companies are increasingly digitized, making them vulnerable to cyberattacks. A successful attack on transportation infrastructure could disrupt supply chains, delay goods and passengers, and cause significant economic losses across multiple industries. The financial impact would include operational recovery costs, compensation for delays, and long-term damage to global trade flows. The recent disruptions to major shipping lines due to cyber incidents highlight this acute vulnerability.
Healthcare Systems: Patient Data and Service Disruption
Healthcare organizations hold vast amounts of sensitive patient data, making them attractive targets for ransomware and data theft. The financial implications include ransom payments, significant fines for HIPAA violations, and the immense cost of restoring patient records and operational systems. More critically, attacks can disrupt patient care, leading to canceled appointments, delayed surgeries, and even adverse health outcomes, which can result in costly malpractice lawsuits and severe reputational damage. The blend of sensitive data and critical services makes the cybersecurity financial impact particularly complex and devastating.
Mitigating the Financial Impact: Strategies for 2026
Addressing the escalating cybersecurity financial impact requires a multi-pronged, proactive approach. Organizations and governments must invest strategically in resilience, threat intelligence, and a culture of security.
Robust Cybersecurity Frameworks and Best Practices
Implementing comprehensive cybersecurity frameworks like NIST CSF (National Institute of Standards and Technology Cybersecurity Framework) is fundamental. These frameworks provide a structured approach to identifying, protecting, detecting, responding to, and recovering from cyber threats. Adhering to best practices such as multi-factor authentication, regular security audits, patching vulnerabilities promptly, and network segmentation can significantly reduce the attack surface and limit the damage of successful breaches. Continuous assessment and adaptation of these frameworks are crucial given the dynamic threat landscape.
Advanced Threat Detection and Response (ATDR)
Traditional perimeter defenses are no longer sufficient. Organizations need to invest in advanced threat detection and response capabilities, including Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), and Extended Detection and Response (XDR) solutions. These technologies leverage AI and machine learning to identify anomalous behavior, detect sophisticated threats early, and automate response actions, thereby minimizing the dwell time of attackers and reducing the overall cybersecurity financial impact of an incident.
Cybersecurity Insurance and Risk Transfer
While not a substitute for robust security, cybersecurity insurance plays a crucial role in mitigating the financial fallout from a breach. Policies can cover costs associated with incident response, legal fees, data recovery, business interruption, and even ransom payments (though this remains a contentious issue). Organizations should carefully evaluate their coverage, understand policy exclusions, and ensure their security posture aligns with insurer requirements. Transferring some of the financial risk through insurance is a prudent strategy in today’s threat environment.

Supply Chain Security and Third-Party Risk Management
Given the increasing threat of supply chain attacks, organizations must implement rigorous third-party risk management programs. This includes thorough vetting of vendors, contractual requirements for cybersecurity standards, regular security assessments of suppliers, and continuous monitoring of their security posture. Understanding and managing the vulnerabilities introduced by third-party providers is critical to preventing cascading breaches and limiting the broader cybersecurity financial impact.
Workforce Training and Cyber Awareness
Human error remains a leading cause of cyber incidents. Comprehensive and continuous cybersecurity awareness training for all employees is essential. This includes educating staff about phishing, social engineering, strong password practices, and safe browsing habits. A well-informed workforce can act as the first line of defense, significantly reducing the likelihood of successful attacks and thereby mitigating potential financial losses. Regular simulations and phishing tests can reinforce these training efforts.
Public-Private Partnerships and Information Sharing
Addressing national-level cybersecurity threats requires collaboration between government agencies and private sector entities. Information sharing frameworks, such as those facilitated by CISA (Cybersecurity and Infrastructure Security Agency), enable organizations to share threat intelligence, attack methodologies, and best practices. This collective defense approach helps to build a more resilient ecosystem, allowing for faster detection and response to emerging threats, and ultimately reducing the collective cybersecurity financial impact on U.S. infrastructure.
The Economic Imperative of Cybersecurity Investment
The financial world operates on trust and stability. Cyberattacks, particularly those targeting critical infrastructure, erode both. The projected cybersecurity financial impact in 2026 is not merely an operational cost; it is an economic imperative. Underinvestment in cybersecurity now will inevitably lead to far greater financial losses in the future. Governments and organizations must view cybersecurity not as a cost center but as a strategic investment in economic stability, national security, and long-term prosperity.
The cost of prevention, while significant, pales in comparison to the potential costs of recovery from a major cyber catastrophe. A proactive stance, embracing advanced technologies, fostering a culture of security, and engaging in collaborative defense, are all non-negotiable elements in safeguarding U.S. infrastructure from the financial devastation of cyber threats. As the digital battleground expands, so too must our commitment to robust and resilient cybersecurity defenses, ensuring that the economic engine of the United States remains secure and operational.
Future Trends and Continuous Adaptation
Looking beyond 2026, the cybersecurity landscape will continue to evolve. The advent of quantum computing poses a potential threat to current encryption standards, necessitating research into quantum-resistant cryptography. The increasing deployment of Artificial Intelligence (AI) and Machine Learning (ML) will also be a double-edged sword, offering powerful defensive capabilities but also empowering attackers with more sophisticated tools for automation and evasion. Organizations must therefore embed a principle of continuous adaptation and innovation into their cybersecurity strategies to stay ahead of emerging threats.
This includes fostering a culture of continuous learning within cybersecurity teams, investing in advanced research and development, and actively participating in cybersecurity communities and forums to stay abreast of the latest threat intelligence and defensive techniques. The dynamic nature of cyber threats means that static security postures are invitations to disaster. Only through perpetual vigilance and strategic investment can the U.S. hope to mitigate the profound and escalating cybersecurity financial impact on its vital infrastructure.
Conclusion: A Call to Action for U.S. Infrastructure Resilience
The year 2026 looms as a critical juncture for U.S. critical infrastructure, where the confluence of advanced cyber threats and increasing digital dependency could lead to unprecedented financial repercussions. The direct and indirect costs of cyber breaches – from incident response and regulatory fines to reputational damage and lost intellectual property – paint a grim picture of potential economic instability. The pervasive and escalating cybersecurity financial impact demands a unified and strategic response from all stakeholders.
Protecting our nation’s vital systems is not merely a technical challenge; it is an economic imperative. By prioritizing robust cybersecurity frameworks, investing in advanced threat detection, embracing risk transfer mechanisms like cyber insurance, securing supply chains, and empowering a cyber-aware workforce, the U.S. can build a more resilient infrastructure. Furthermore, fostering strong public-private partnerships and promoting information sharing are essential for a collective defense strategy capable of countering global threats.
The financial stability and national security of the United States depend on our ability to effectively anticipate, prevent, and respond to cyberattacks. The time to act decisively and strategically is now, ensuring that the critical infrastructure that underpins our society and economy remains secure against the evolving digital dangers of 2026 and beyond.





