Cyber Warfare in 2025: Protecting US Critical Infrastructure
Anúncios
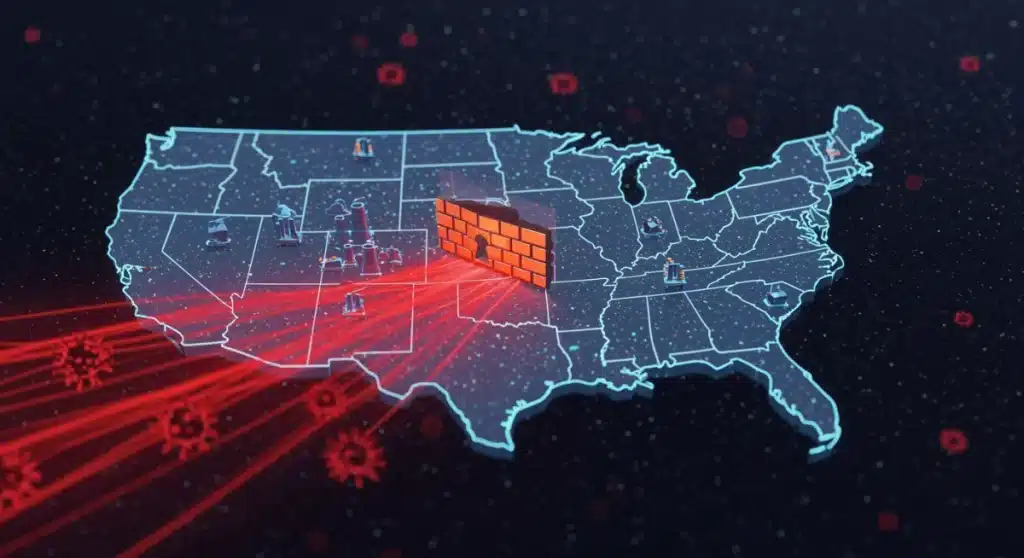
By 2025, cyber warfare against US critical infrastructure will intensify, demanding robust, multi-layered defenses to counter advanced state-sponsored threats and safeguard national security and public services.
Anúncios
The landscape of global conflict is rapidly evolving, with digital battlegrounds becoming as critical as physical ones. In 2025, the threat of cyber warfare infrastructure attacks on US critical infrastructure by state-sponsored actors looms larger than ever, demanding immediate and strategic attention. This isn’t merely a technological challenge; it’s a profound national security imperative that touches every aspect of American life, from power grids to financial systems.
The Evolving Threat Landscape of Cyber Warfare
The nature of cyber warfare is dynamic, constantly adapting to new technologies and geopolitical shifts. In 2025, state-sponsored actors possess sophisticated capabilities, moving beyond simple data breaches to targeted, disruptive attacks aimed at crippling essential services. These adversaries often operate with significant resources, advanced persistent threats (APTs), and a willingness to exploit any vulnerability.
Anúncios
Understanding the motivations behind these attacks is crucial for developing effective defenses. Geopolitical rivalry, economic espionage, and the desire to sow discord are primary drivers. Nations like Russia, China, Iran, and North Korea have been consistently identified as significant threats, each with unique methodologies and objectives. Their efforts are often highly coordinated, blending cyber operations with traditional intelligence gathering.
Advanced Persistent Threats (APTs)
APTs represent a particularly insidious form of cyber attack. Unlike typical malware, APTs are designed for long-term infiltration, remaining undetected for extended periods while exfiltrating data or preparing for disruptive actions. They often leverage zero-day exploits and highly customized tools, making detection and eradication exceptionally difficult.
- Stealth and Persistence: APTs prioritize remaining hidden, often using legitimate system tools to blend in.
- Targeted Operations: They focus on specific high-value targets within critical infrastructure.
- Resource-Intensive: Developing and deploying APTs requires significant state-level resources and expertise.
The continuous evolution of these threats necessitates a proactive and adaptive defense posture. Relying solely on reactive measures is no longer sufficient; a predictive and intelligence-driven approach is paramount to stay ahead of these determined adversaries.
Identifying US Critical Infrastructure Vulnerabilities
The United States’ critical infrastructure is a vast, interconnected web of systems vital for national security, economic prosperity, and public health and safety. This infrastructure, however, presents numerous vulnerabilities that state-sponsored adversaries are eager to exploit. The sheer complexity and age of some systems, coupled with the increasing reliance on digital controls, create a fertile ground for cyber incursions.
Sectors such as energy (electricity grids, oil, and gas pipelines), water and wastewater systems, transportation (air, rail, maritime), communications, healthcare, and financial services are particularly at risk. Many of these systems were not designed with modern cybersecurity threats in mind, and their integration with IT networks has introduced new attack vectors.
Legacy Systems and Interdependencies
A significant portion of critical infrastructure still relies on legacy operational technology (OT) systems that are difficult to update, patch, or secure. These older systems often lack modern security features and can serve as entry points into broader networks. Moreover, the interdependencies between different sectors mean that a successful attack on one can cascade into others, causing widespread disruption.
- Outdated Software: Many industrial control systems (ICS) and supervisory control and data acquisition (SCADA) systems run on old software.
- Lack of Segmentation: OT networks are often not sufficiently separated from IT networks, increasing exposure.
- Supply Chain Risks: Vulnerabilities can be introduced through hardware, software, or services from third-party vendors.
Addressing these vulnerabilities requires a comprehensive strategy that includes modernizing infrastructure, implementing robust segmentation, and rigorously vetting supply chains. It’s a continuous process of assessment, mitigation, and adaptation to emerging threats.
Strategic Defense: Government and Private Sector Collaboration
Protecting US critical infrastructure from cyber warfare in 2025 is not a task the government can undertake alone. It demands unprecedented collaboration between federal agencies, state and local governments, and the private sector. The vast majority of critical infrastructure is privately owned and operated, making their active participation indispensable for national cybersecurity.
Initiatives like the Cybersecurity and Infrastructure Security Agency (CISA) play a pivotal role in fostering this collaboration, providing guidance, resources, and threat intelligence. Information sharing is paramount, allowing organizations to learn from each other’s experiences and collectively raise the bar for defense. Trust and clear communication channels are foundational to effective partnerships.
Information Sharing and Threat Intelligence
Real-time information sharing about emerging threats, vulnerabilities, and attack methodologies is critical. Government agencies can provide classified intelligence, while the private sector can offer insights into the practical realities of system operations and attack impacts. This symbiotic relationship enables a more holistic and informed defense strategy.
- CISA’s Role: Acts as a central hub for cybersecurity information and coordination.
- ISACs: Information Sharing and Analysis Centers facilitate sector-specific threat intelligence exchange.
- Joint Exercises: Simulated cyberattack scenarios help test and refine response plans across sectors.
Building a resilient defense ecosystem hinges on breaking down silos and fostering a culture of shared responsibility. This means establishing clear protocols for incident reporting, coordinated response mechanisms, and continuous training across all levels of government and industry.

Technological Innovations in Cybersecurity Defenses
As state-sponsored cyber threats grow more sophisticated, so too must the defensive technologies. Innovation in cybersecurity is a continuous arms race, with new tools and techniques emerging to counter evolving attack methods. In 2025, advanced technologies are at the forefront of protecting critical infrastructure, offering capabilities that were once the realm of science fiction.
Artificial intelligence (AI) and machine learning (ML) are transforming threat detection, enabling systems to identify anomalous behavior and potential attacks with greater speed and accuracy than human analysts alone. Quantum-resistant cryptography is also gaining traction as a long-term solution against future quantum computing threats that could break current encryption standards.
AI and Machine Learning for Threat Detection
AI and ML algorithms can analyze vast datasets of network traffic, system logs, and threat intelligence to identify patterns indicative of a cyber attack. They can detect zero-day exploits, insider threats, and sophisticated malware that might bypass traditional signature-based defenses. This proactive detection significantly reduces the time adversaries have to cause damage.
- Behavioral Analytics: AI can establish baselines for normal system behavior and flag deviations.
- Automated Response: ML-driven systems can initiate automated containment or mitigation actions.
- Predictive Capabilities: AI can anticipate potential attack vectors based on historical data and current threat intelligence.
While these technologies offer immense promise, they also come with challenges, such as the need for vast training data and the risk of adversarial AI techniques. Continuous research and development are essential to harness their full potential while mitigating their limitations.
Policy and Regulatory Frameworks for Cyber Resilience
Effective cybersecurity is not just about technology; it’s also about establishing robust policy and regulatory frameworks. In 2025, the US government continues to refine its approach to cyber resilience, recognizing that clear mandates, incentives, and accountability are crucial for protecting critical infrastructure. These frameworks aim to standardize security practices, encourage investment in defenses, and ensure a coordinated national response to cyber incidents.
Recent legislative efforts and executive orders have focused on improving information sharing, enhancing supply chain security, and establishing baseline cybersecurity requirements for critical sectors. These policies often balance regulatory burdens with the need for flexibility, acknowledging the diverse nature of infrastructure operators.
Key Policy Initiatives
Several policy initiatives are shaping the cybersecurity landscape for critical infrastructure. These include mandatory reporting requirements for cyber incidents, guidelines for implementing zero-trust architectures, and programs to support workforce development and skill building in cybersecurity.
- Cyber Incident Reporting: Mandates for critical infrastructure entities to report significant cyber incidents.
- Zero Trust Architecture: Promoting a security model that assumes no implicit trust, regardless of location.
- Supply Chain Security: Regulations to assess and mitigate risks within the digital supply chain.
The ongoing development and enforcement of these policies are vital. They provide the necessary structure to guide organizations in their cybersecurity efforts, ensuring a baseline level of protection across the nation’s most vital assets. However, these policies must remain adaptable to the rapidly changing threat environment.
Building a Resilient Cyber Workforce and Culture
Ultimately, technology and policy are only as effective as the people who implement and manage them. Building a resilient cyber workforce and fostering a strong cybersecurity culture are paramount to protecting US critical infrastructure in 2025. The current shortage of skilled cybersecurity professionals is a significant national security concern, requiring concerted efforts to recruit, train, and retain talent.
Beyond technical expertise, a strong cybersecurity culture emphasizes awareness, vigilance, and proactive security practices at all levels of an organization. Every employee, from the C-suite to frontline operators, plays a role in maintaining cyber hygiene and recognizing potential threats. Human error remains one of the most common vectors for cyber attacks, making continuous training and awareness programs essential.
Cybersecurity Education and Training
Investing in education and training programs is critical to addressing the talent gap. This includes promoting STEM education from an early age, developing specialized cybersecurity curricula in universities, and offering reskilling opportunities for existing professionals. Public-private partnerships can help bridge the gap between academic learning and industry needs.
- Academic Programs: Developing specialized degrees and certifications in cybersecurity.
- Apprenticeships: Hands-on training programs to build practical skills.
- Continuous Learning: Regular professional development to keep skills current with evolving threats.
Cultivating a culture where cybersecurity is everyone’s responsibility requires consistent communication, clear policies, and leadership commitment. By empowering individuals with the knowledge and tools to be cyber-aware, organizations can significantly strengthen their overall defense posture against state-sponsored aggressors.
| Key Aspect | Brief Description |
|---|---|
| Evolving Threats | State-sponsored actors employ advanced persistent threats (APTs) targeting critical infrastructure. |
| Infrastructure Vulnerabilities | Legacy systems, interdependencies, and supply chain risks create significant exposure. |
| Collaboration & Policy | Government-private sector partnerships and strong regulatory frameworks are essential. |
| Cyber Workforce | Addressing the talent gap and fostering a cyber-aware culture are critical for resilience. |
Frequently Asked Questions About Cyber Warfare & Infrastructure
State-sponsored cyber warfare involves cyber attacks conducted by, or on behalf of, a national government. These attacks often target critical infrastructure, government networks, or key industries of rival nations, aiming to achieve strategic objectives like espionage, disruption, or economic sabotage. They are characterized by high sophistication and extensive resources.
US critical infrastructure is a prime target due to its vital role in national security, economic stability, and public welfare. Disrupting sectors like energy, finance, or communications can cause widespread chaos, undermine public trust, and weaken a nation’s ability to respond to crises, offering significant leverage to adversaries.
AI and machine learning enhance cybersecurity defenses by enabling faster and more accurate threat detection. They can analyze vast amounts of data to identify anomalous patterns, predict potential attack vectors, and automate responses, thereby significantly reducing the time attackers have to cause damage and improving overall system resilience.
The private sector plays a crucial role as it owns and operates the majority of US critical infrastructure. Their collaboration with government agencies through information sharing, adherence to cybersecurity best practices, and investment in robust defenses is indispensable for creating a comprehensive national cybersecurity posture against state-sponsored threats.
The biggest challenges include the prevalence of legacy systems, complex interdependencies across sectors, a significant shortage of skilled cybersecurity professionals, and the constantly evolving sophistication of state-sponsored threats. Addressing these requires continuous investment, innovation, and a unified national effort across all stakeholders.
Conclusion
The imperative to protect US critical infrastructure from state-sponsored cyber warfare in 2025 is a multifaceted challenge demanding a holistic and dynamic response. It requires not only cutting-edge technological defenses and robust policy frameworks but also an unwavering commitment to collaboration between government and the private sector, underpinned by a highly skilled and cyber-aware workforce. As the digital battleground continues to expand, the nation’s resilience will depend on its ability to adapt, innovate, and unite against these pervasive and evolving threats, safeguarding the foundational elements of American society and economy.





